DANGER…there is an identity thief sitting in your office, right now. It’s lurking in a hidden corner, silently capturing confidential information about your employees, your customers, and your company’s financial situation. It’s gathering social security numbers, bank account numbers, credit card numbers, personal data and more right before your very eyes. Who is it? It’s your copy machine.
Most modern-day copy machines contain a hard drive that when activated, stores every image that runs through its system. This information can be a treasure trove for a thief. If it makes its way to the identity-theft black market, you as a business owner can be held liable, subject to fines, legal action, or worse.
Here are the following steps you can take right now to mitigate the risk…
- Know Your Vendors. Thieves will pay copy machine repair personnel to activate a hard drive, and later, download the information to be shared with the thief. Make sure you select a vendor that is well known in your community, has a stellar reputation, and screens employees.
- Regularly Erase Your Machine’s Hard Drive. Read your copy machine’s manual and learn how to erase its hard drive—it’s usually fairly easy. Have someone in your office put it on his or her calendar to erase the disk weekly. Some newer models allow you to encrypt any stored data; see if your model offers that option (you may need to pay a small fee) and if yes, activate it.
- Search and Destroy. Companies often lease a copy machine, or if they do own it, sell it after a few years. These used machines—with their fully-loaded hard drives—are often resold via auction to unknown buyers, and then shipped overseas where they could end up in the hands of professional identity thieves. Before you get rid of your copy machine, make sure that you reformat its hard drive to completely erase any stored data.
Business identity theft is serious business. In fact, it can financially damage a small company quickly as the fines and legal repercussions can be immense if a data breach occurs, not to mention the negative publicity and severe reputation damage that ultimately results in lost business.
Can a business fully protect itself from a data breach occurring? Unfortunately, no, although following the steps highlighted above is a great place to start.
Small businesses can now purchase identity theft plans at a surprisingly affordable cost. The better plans offer features such as constant monitoring and 360 degree view of a company’s credit and reputation; instant alerts notifying if any of a company’s information is being traded on the internet black market; custom breach plans; and most important, a full remediation package that will manage the legal and reputation requirements necessary if a theft occurs.
Sam Richter is the founder of the #1-rated Know More! business improvement program and is considered one of the world’s leading experts on online information. For more information about Sam, his books/videos, and his presentations, please visit his website and get his free identity theft guide.
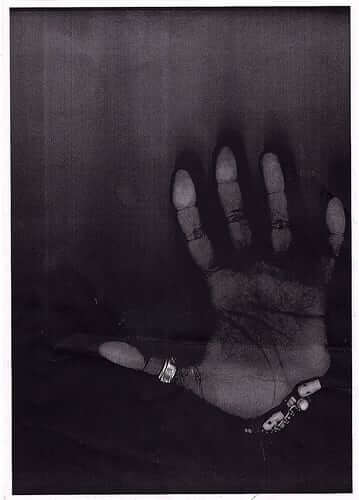
Photo credit: 0uT$!d£r